Pirate,
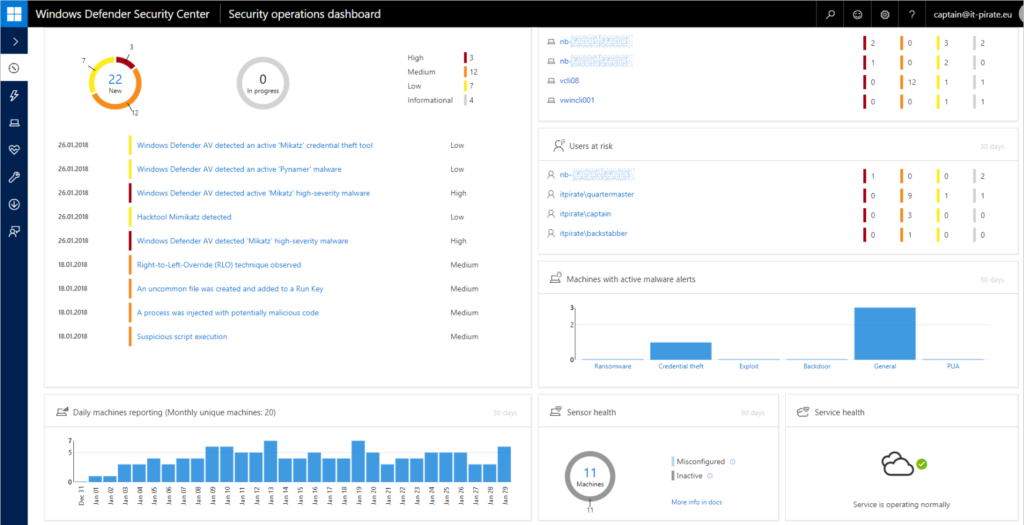
within the last year, we have focused on Windows Defender ATP and ran through several PoCs. I’ve prepared several scenarios for you, where I will guide you trough WDATP from the tenant creation to high end scenarios. In this first post, we will go through the tenant creation process itself.
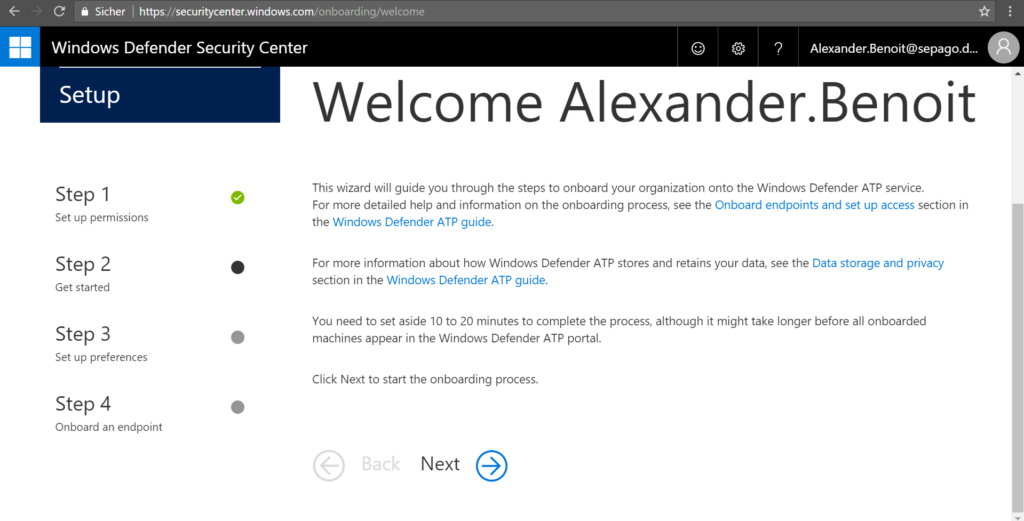
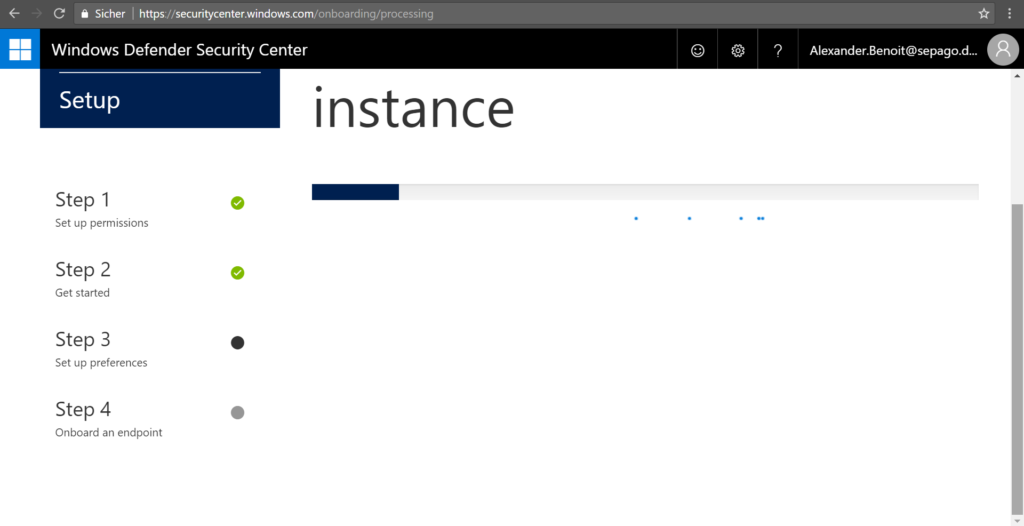
Microsoft offers a 90 day trial of WDATP that can be requested here. Within this time frame, you may test the full feature set including pre-breach and post-breach protection. After you’ve accepted the “Microsoft Trial Online Service Terms for Windows Defender Advanced Threat Protection” and entered your personal details, the request will run through the workflow and (hopefully) will be accepted. You will then receive a link that brings you right to https://securitycenter.windows.com/onboarding/welcome ,where you may start your onboarding process:
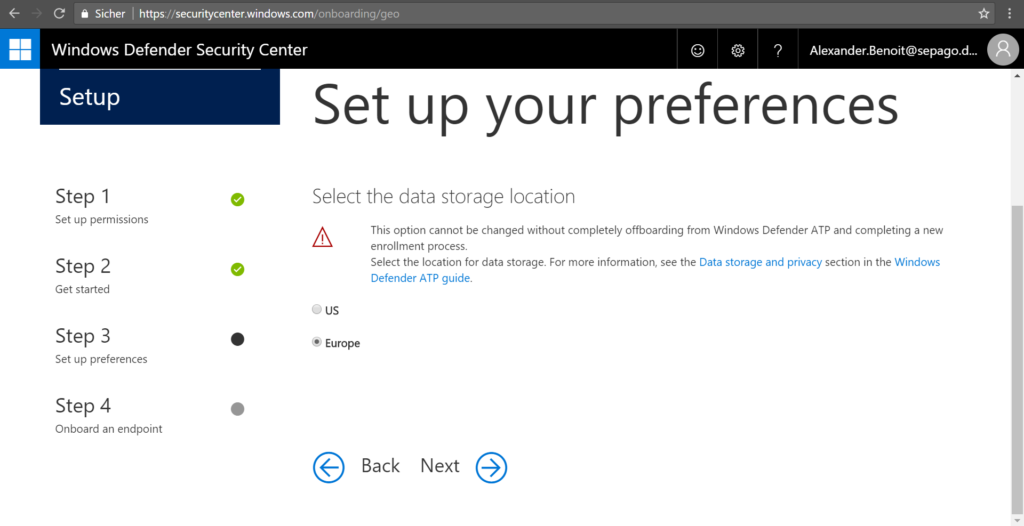
One of the most important steps (especially for us in Germany 🙂 ) is the data storage location. Therefore, Microsoft has created a docs article called “Windows Defender ATP data storage and privacy“. If you are about to get started with WDATP or any Threat Intelligence product, you should give it a read. Urgent questions such as
- What data does WDATP collect?
- Can I decide where my data is stored?
- How does Microsoft prevent malicious insider activities and abuse of high privilege roles?
- Is data shared with other customers?
are answered in this article. So set up your data storage location. Choose carefully, this setting can not be changed once the instance has been created.
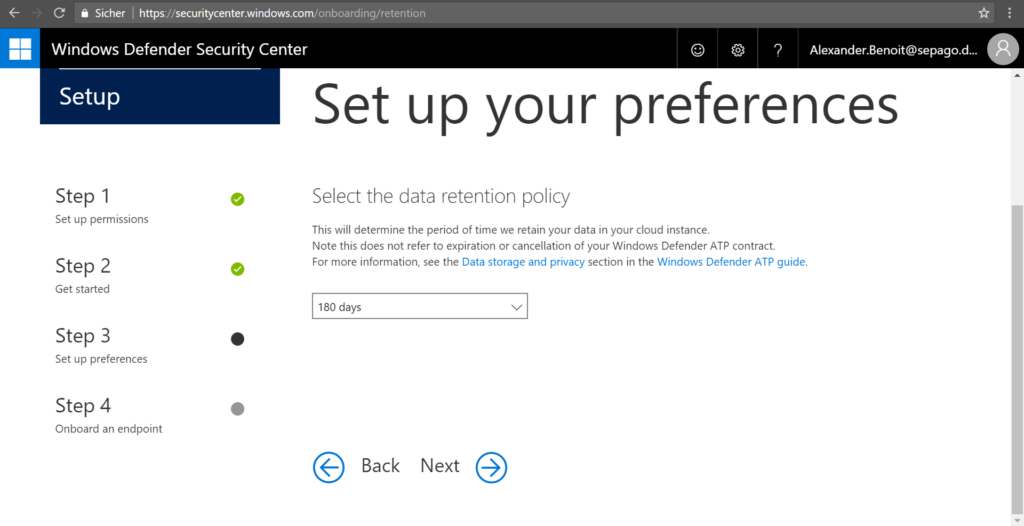
…and your data retention policy. In other words, you can configure how long threats and information that got detected on any machine will be saved in your tenant. By default, it’s 180 days which can be changed afterwards.
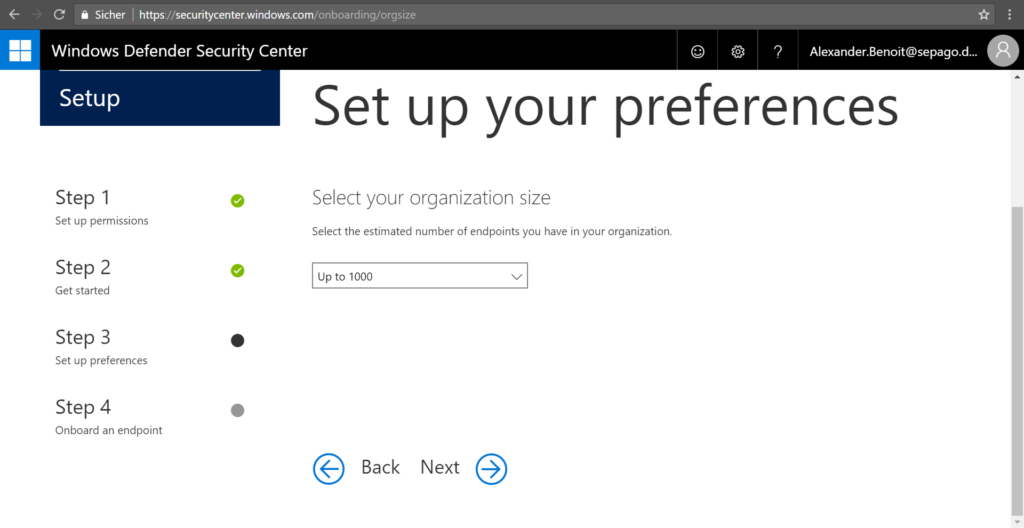
Next up you can configure your organization size. As far as I know thats just an indicator for the Microsoft team to estimate the expected client amount that will show up. The size of your organziation can not be changed afterwards.
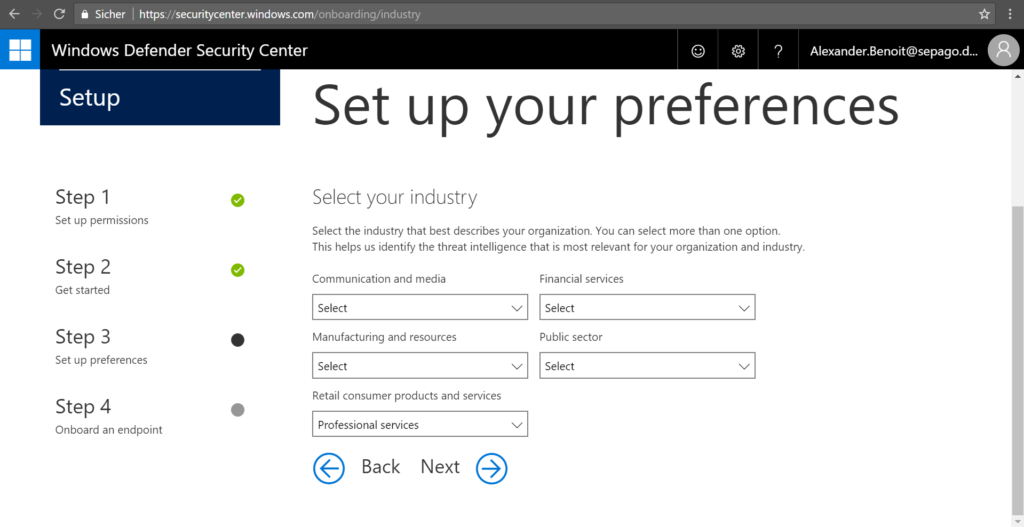
Another big one is the industry configuration. Here Microsoft enrichs your own data with industry specific information. So let’s say your business is healthcare. If you choose Public Sector and Health, the threat intelligence for that vertical will be applied. To understand why this is useful, you have to understand how Microsoft’s Intelligent Security graph works. In a very abstract perspective, it’s all about data and relations between entities. So the power behind WDATP lies in the huge amount of data fed by sensors that report into the huge data pool. The solution then brings information and activities in relation to each other. Additional information is added by other consumer and commercial services (like Azure AD, Office 365, Bing, etc). Then, the solution gets processed by big data and machine learning mechanisms. There’s one more thing coming in on top: Microsoft calls it “Microsoft unique optics”. And that (in short) not only gives you the insight into whats going on in your environment, but adds a industry-specific threat intelligence aspect. This gives you all the more reason to set it up properly. By the way, you can select more than one category and the selected options can be changed afterwards.
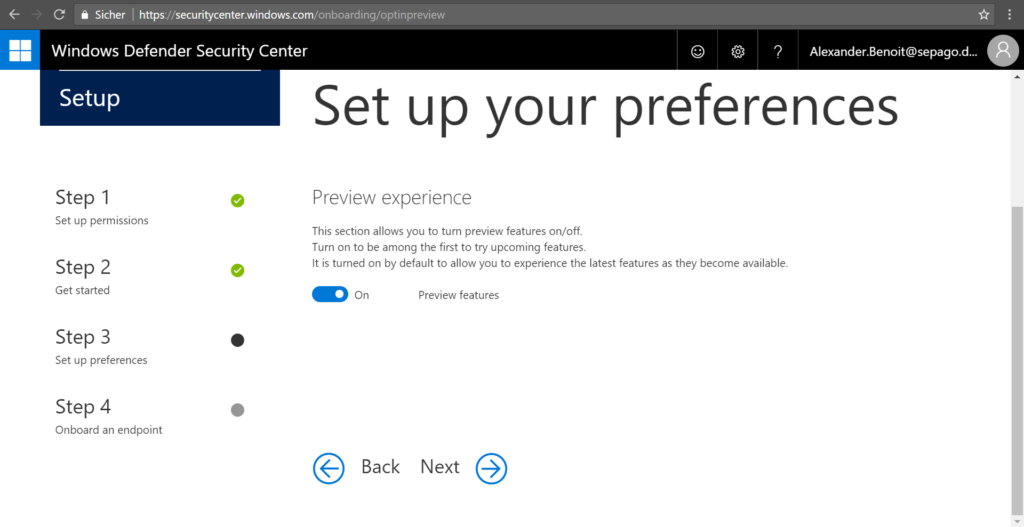
Like nearly every service, Windows Defender ATP service is constantly being updated to include new feature enhancements and capabilities. If you want preview experience (and I highly recommend this, especially when doing a PoC) you can turn it on here. You’ll then have access to upcoming features, for which you can provide feedback.
Read more on preview features at docs.microsoft.com.
Like mentioned before, the data storage location and the organization size cannot be changed once the instance has been created.
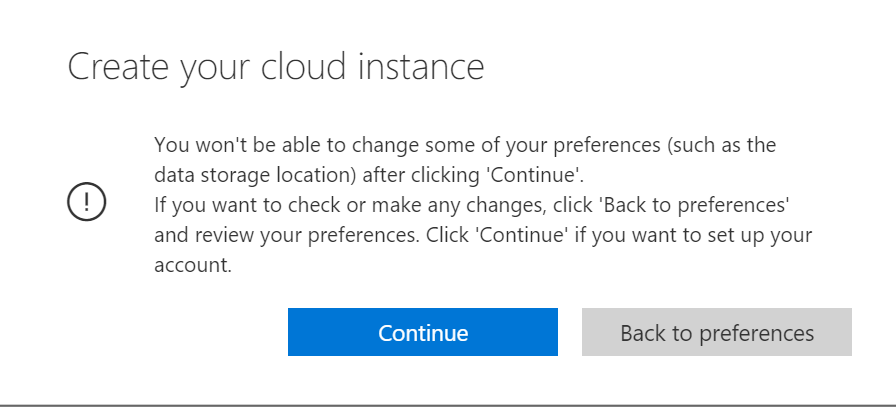
Your instance will be created after you’ve clicked continue.
Next up: onboarding of machines.
Yaaaaaaaaar!
*Cap.
Submit a comment on “Windows Defender ATP: Tenant creation – Part 1”