Microsoft Purview: Deploy Labels like a Hero (feat. Microsoft Entra)
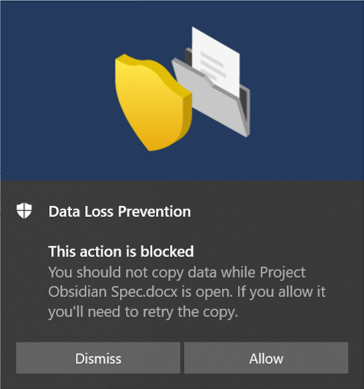
In what follows we proceed to talk about the co-working between Microsoft Entra (Azure AD; PIM) and Microsoft Purview. The aim is to present the possibilities of leveraging PAM to deploy labels, policies and similar to mail-enabled groups (M365 Group for this post).
Please do not see this as a limitation, rather, the possibility to use this tech in scenarios that require a mail-enabled group to be assigned for example, when assigning super users, creating test DLP policies, etc., or in this case deploying labels like a hero! TBH the possibilities are endless.
What is Microsoft Entra?
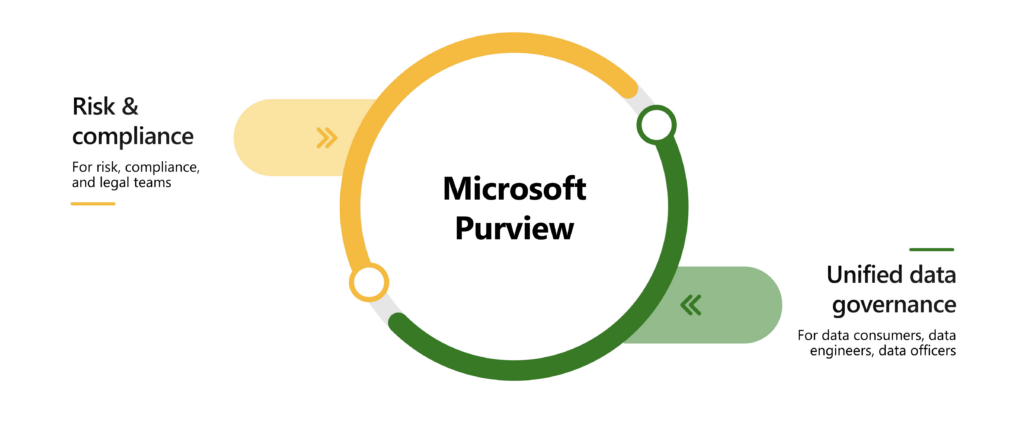
Recently reorganized enters Microsoft Entra (refer launch post under link), now defined as the product family encompassing all of MSs’ identity and access capabilities. This family now comprises the following three products (two of which are new):
- Microsoft Azure Active Directory (Azure AD)
- Cloud Infrastructure Entitlement Management (CIEM)
- Decentralized Identity
The products in the Entra family will help provide secure access to everything for everyone, by providing identity and access management, cloud infrastructure entitlement management, and identity verification.
Microsoft Entra will verify all types of identities and secure, manage, and govern their access to any resource. The new Microsoft Entra product family will:
- Protect access to any app or resource for any user.
- Secure and verify every identity across hybrid and multi-cloud environments.
- Discover and govern permissions in multi-cloud environments.
- Simplify the user experience with real-time intelligent access decisions.
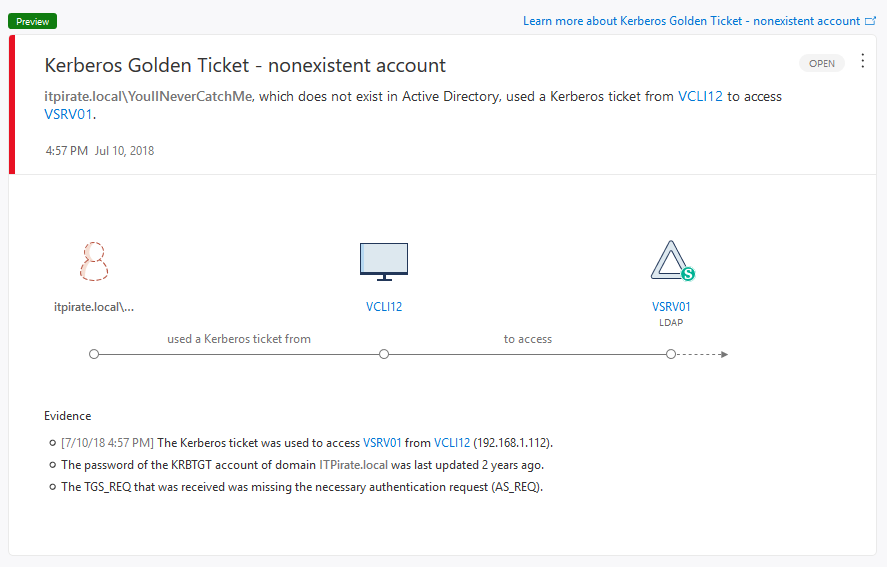
The specific part of Entra we will use for this solution is Azure AD, finer granularly PIM (Privileged Identity Management). To be clear, one of the pivotal parts of this solution utilizes a feature called “Privileged Access Groups” which is still in preview at the time of writing this post.