Pirate,
in June 2018, Mark Simos who works as Lead Architect, Enterprise Cybersecurity Group at Microsoft published the updated “Cybersecurity Reference Architecture”. I find this a very valuable collection of architectural information as it often gives a good impression of the big picture approach. As there is a webcast coming up, where Mark is going to explain the design and how you as a architect or systems engineer can use this reference architecture, I decided to wrap that information up in a blogpost.
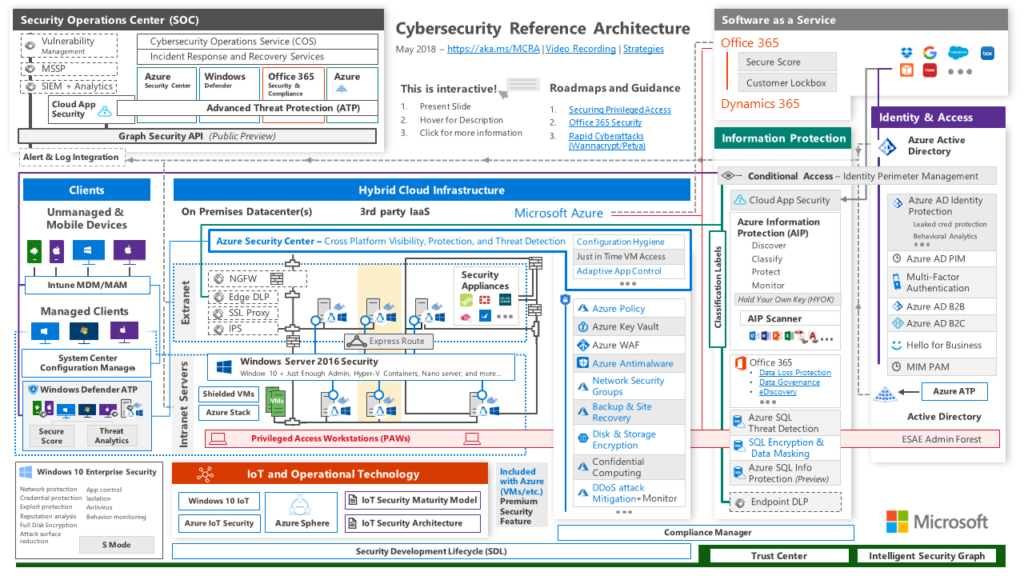
The Microsoft cyber-security Reference Architecture describes Microsoft’s cyber-security capabilities and how they integrate with existing security architectures and capabilities. You can download it here: Microsoft Cybersecurity Reference Architecture
It’s actually version 2 of this overview and a lot has changed since version one. There’s a good overview of everything that was added on this blog by Mark Simons: Cybersecurity Reference Architecture: Security for a Hybrid Enterprise
If you want to learn more than that – like how you can use it for example, check out this webcast: Learn About Version 2 Of The Microsoft Cybersecurity Reference Architecture (MCRA)! (M365v121PAL) it will be hold on Thursday, August 23, 2018. In this webcast you can learn how you can use this document in your customer conversations to help show the breadth and depth of the Microsoft cyber-security portfolio. You’ll learn what’s new since v1 and how to present Microsoft’s cyber-security story using the MCRA deck. This is also your chance to ask questions about the MCRA.
And there’s even more! Mark has written down a good set of information in the so called: Mark’s List which you can find here: https://www.linkedin.com/pulse/marks-list-mark-simos/
Although not everything is up to date anymore you can find a lot of useful stuff there. I personally love the Mitigating Rapid Cyberattacks (Petya, WannaCrypt, and similar) slides and Microsoft Cybersecurity Reference Architecture
Enjoy!
*Cap
Submit a comment on “Microsoft Cybersecurity Reference Architecture”